We are currently navigating the transition from conversational AI to Agentic AI. In 2026, the core question is no longer whether large language models are smart enough, but whether AI can truly take over workflows in a live production environment.
Imagine an AI agent executing a cross-cloud migration for a client. For the first two hours, it perfectly configures VPCs between AWS and GCP, provisions instances, and at Step 12, modifies the legacy database. Then, at Step 13, it crashes due to a rare API rate limit.
What do you do? If you retry, it might alter the database again. If you restart, it has no memory of the instances it already spun up. Without effective state recovery, your entire cloud environment is now a catastrophic mess.
This is a highly realistic scenario. Any agent running more than 10 consecutive steps in production will encounter similar structural issues. As Dai Guanlan (Founder & CEO of Runta) recently outlined, existing infrastructure is fundamentally unequipped to solve this, and a new paradigm is required.
The Five Unique Execution Traits of Agents
Most teams treat agents as simple LLM wrappers, attaching a few tool calls and harnesses before pushing them to production. But when you grant an agent real system permissions and let it run autonomously, its execution profile looks nothing like traditional software.
Production agents possess five distinct attributes:
- Long-Horizon Execution: Crashing is a statistical certainty over long runtimes.
- Hostile Inputs: Similar to client-side JavaScript in a browser, the text an agent processes (emails, web pages, API responses) may contain prompt injections. You must assume all inputs are untrusted.
- Real Permissions: Agents hold API keys, database credentials, and cloud platform tokens.
- Non-Deterministic Decisions: The same prompt can yield a different execution path at a different time due to the probabilistic nature of LLMs.
- Real Side Effects: Every step alters the real world. Sent emails cannot be unsent; deleted database records cannot be easily restored.
The recent viral success of open-source coding agents like OpenClaw has pushed this reality to the forefront. Granting models real system access brings a leap in capability, but it also turns theoretical security risks into immediate, practical threats.
None of these five traits are novel on their own. Databases use transaction semantics for side effects, browsers use sandboxes for hostile inputs, and distributed systems use checkpoints for long-running tasks. The difficulty with Agentic AI is that it chains all five attributes together, and no off-the-shelf infrastructure was designed for this specific combination.
The Two Misplaced Assumptions of Legacy Infra
Current agent infrastructure is built on two dangerously outdated assumptions:
1. The Threat Model Assumption: The industry is currently running client-side code using server-side security assumptions. We assume that aside from user input, the execution environment is controlled and APIs are safe. In reality, agents read hostile inputs, wield real secrets, and operate in uncontrolled environments. An agent's threat model is a browser, not a server.
2. The Execution Model Assumption: Traditional infrastructure was built for deterministic, short-lived, and stateless tasks (e.g., handling an HTTP request). Conversely, agent execution is probabilistic, long-horizon, and deeply stateful. Forcing an agent into an infrastructure designed for stateless request/response paradigms causes critical failures at scale.
These flawed assumptions result in three missing pillars: no side-effect logging (you can't audit what happened), no recoverable execution state (you can't resume from an interruption), and no isolation boundaries (permissions are exposed to untrusted inputs).
The Three Missing Primitives
To properly support enterprise-grade agents, three new infrastructure primitives must be built in a strict sequence:
1. The Effect Log
This is the foundation. To safely recover from a crash, you must treat the real world's side effects as a write-ahead log.
Before making a side-effect-inducing call, the infra writes an intent record (idempotency keys, blast radius, approval level). Afterward, it writes a completion record (request, response, etags). When recovering, read-only calls can be replayed, but side-effect calls must bypass the external world and simply return the sealed completion record.
Tools must declare interface contracts: is this a pure read (safe to replay), an idempotent write, or an irreversible write (forbidden to replay)? If an agent crashes after dropping a table at Step 12, the Effect Log prevents it from executing the drop command again upon restart.
2. Capability Isolation
With the Effect Log in place, you must define capability boundaries.
Real credentials should never be handed directly to the agent process. Instead, all external access must be mediated through a Capability Gateway. The agent only receives time-bound, scope-limited, instantly revocable temporary tokens. This mimics the browser security model: a browser tab can't access the OS directly, not because the JS promises to behave, but because the architecture physically denies it. Open-source implementations like ClawShell are beginning to practice this exact methodology.
3. Fork Recovery
Agent execution is fundamentally a search process through a graph of possibilities, not a straight line. Every branch needs an independent checkpoint containing a semantic closure (model outputs, tool outputs, Effect Log cursors). This allows you to precisely resume execution from a specific node without starting over, transforming a "dead task" into a clean breakpoint.
From Uptime to Resumability
In the SaaS era, the ultimate metric was Uptime (SLA guarantees via redundancy and self-healing). But for agents, Uptime is a proxy metric. You cannot guarantee a 48-hour autonomous agent will never hit a network glitch.
The primary design goal for agent infrastructure is no longer keeping the machine alive, but preserving the semantic correctness of the execution when it inevitably dies. This is a paradigm shift from "Uptime" to "Resumability." Can the agent re-enter execution at any arbitrary point with its state, context, and environment fully restored? An agent that can crash and cleanly resume is vastly more reliable than one built on the fragile assumption that it will never fail.
The Abstraction Mismatch
Why can't existing orchestration and container tools solve this?
- Kubernetes: Isolates resources and processes, but is blind to tool call semantics. A container cannot tell the difference between an agent making a normal API call and one executing a prompt-injected malicious command.
- Modal and E2B: Provide excellent code execution sandboxes. However, execution isolation is not capability isolation. A clean sandbox can still abuse a real API key.
- Temporal and Netflix Conductor: While excellent for durable execution, these orchestrators fundamentally rely on deterministic code for their replay mechanisms. LLMs are inherently non-deterministic. Furthermore, Temporal assumes the workflow code itself is trusted; it will happily and faithfully execute a prompt-injected attack because it views it as standard logic.
The Epsilla Perspective: Architecting the Entropy Reducer
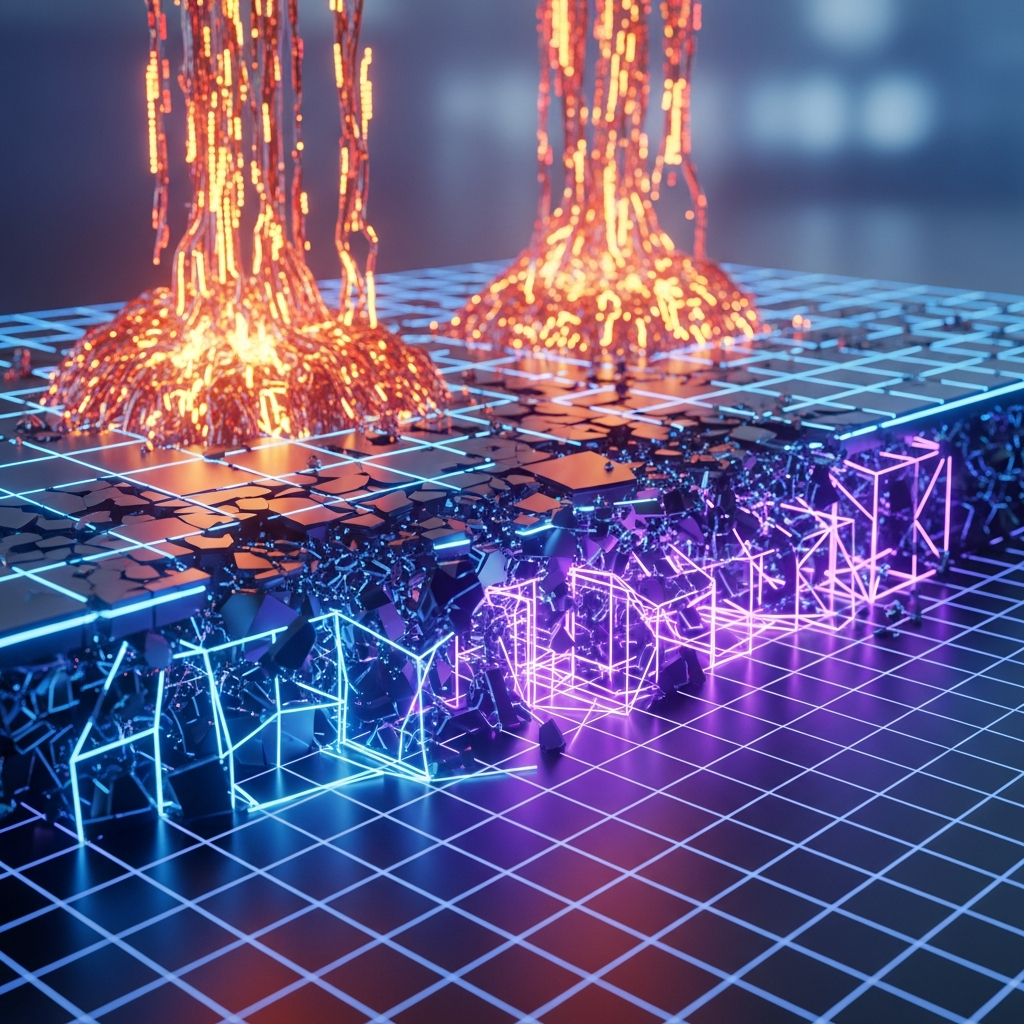
The inherent task of an LLM is to increase entropy (generate novel, probabilistic outputs). The core mission of Agent Infrastructure is to reduce that entropy. The agent decides the behavior; the infrastructure dictates the boundaries.
At Epsilla, we are building AgentStudio to be exactly this kind of entropy-reducing infrastructure. We recognize that as agents transition from short-lived, human-approved tasks to long-horizon, fully autonomous Virtual Team Members, legacy orchestration models will break.
Our Semantic Graph acts as the ultimate enterprise state and memory layer, inherently supporting the complex, graph-based execution recovery that agents require. Furthermore, our Intelligent Gate architecture serves as the exact Capability Gateway needed to dynamically mediate permissions, isolate hostile inputs, and ensure that agents interact with the enterprise's digital nervous system safely.
In the SaaS era, infrastructure solved how to efficiently allocate compute power. In the Agentic era, infrastructure must solve how to safely converge uncertainty. The Agent OS must be rebuilt from the execution layer up.